Documentation Index
Fetch the complete documentation index at: https://qovery-docs-gcp-static-egress-ips.mintlify.app/llms.txt
Use this file to discover all available pages before exploring further.
Creating a GCP GKE Cluster
Connect Your GCP Account
Qovery needs credentials to manage resources in your GCP project. We use a secure service account approach with minimal required permissions.Prepare Your GCP Project
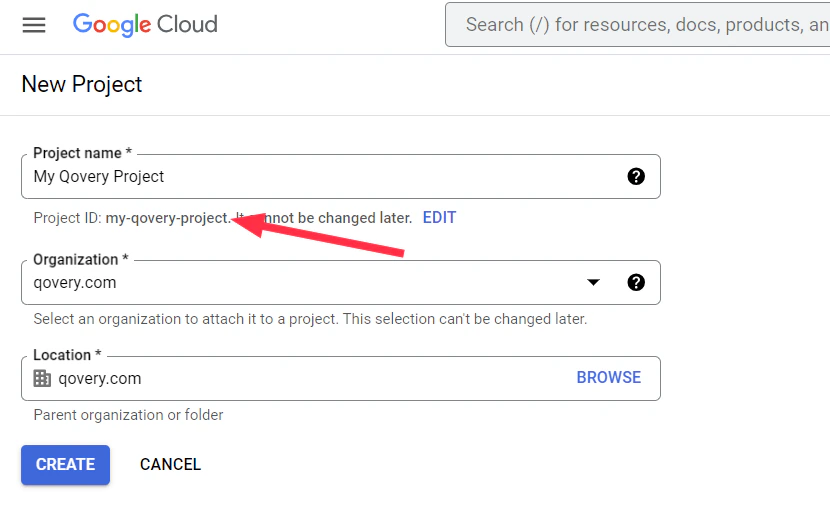
Create or Select Project
- Go to Google Cloud Console
- Either create a new project or select an existing one
- Ensure billing is enabled for the project
Generate Installation Command
Start Cluster Creation
- Go to Qovery Console
- Go to Clusters tab
- Click Create Cluster
- Select GCP as the cloud provider
Enter Project Details
- Enter your Project ID
- Click Next
Run Installation Script
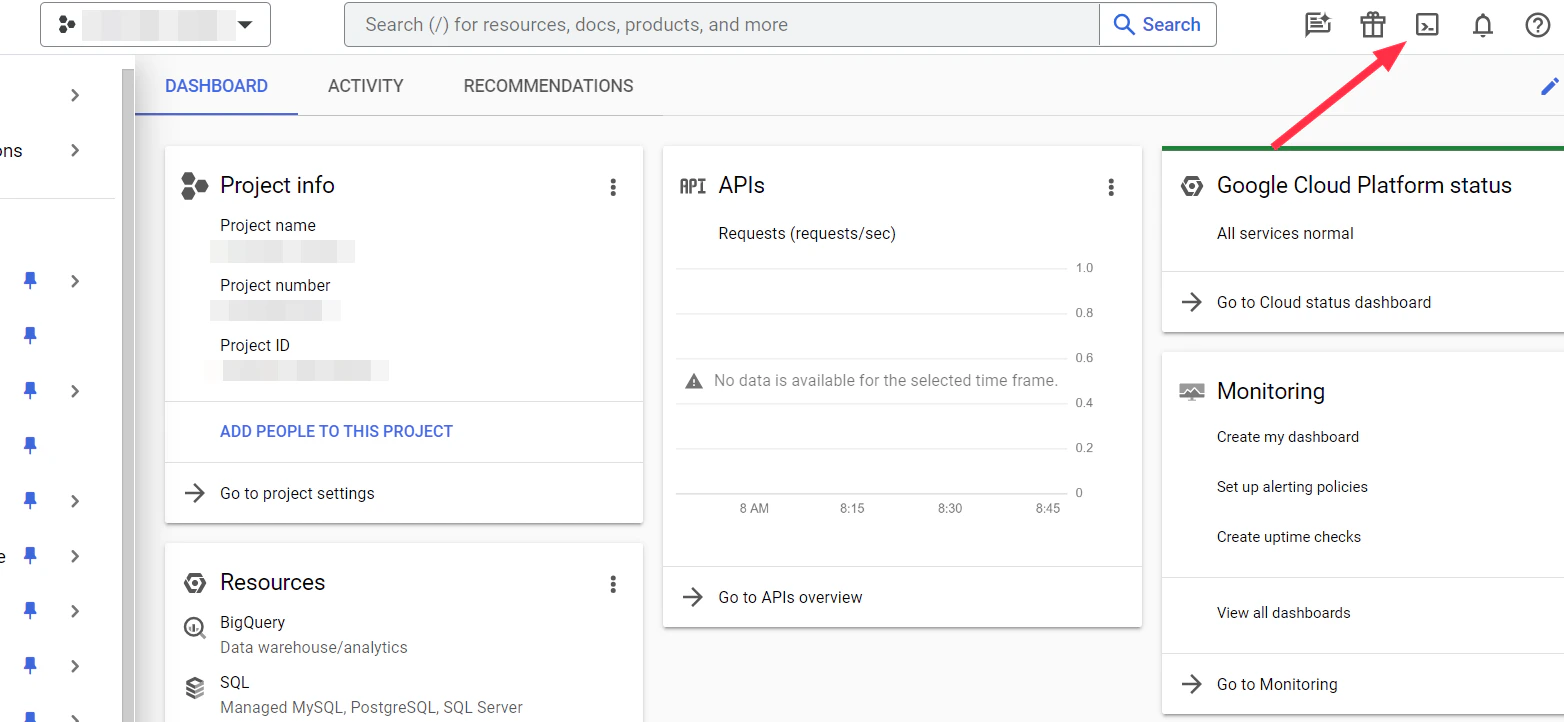
Open Google Cloud Shell
- In Google Cloud Console, click the Cloud Shell icon (terminal icon) in the top-right
- Wait for Cloud Shell to initialize
- Ensure you’re in the correct project:
gcloud config get-value project
Run the Command
- Paste the command from Qovery into Cloud Shell
- Press Enter
- The script will:
- Enable required GCP APIs (Container, Compute, Artifact Registry, Storage, Cloud Resource Manager, Cloud Run)
- Create a service account named
qovery-service-account - Assign necessary IAM roles
- Generate and download a JSON key file (
key.json)
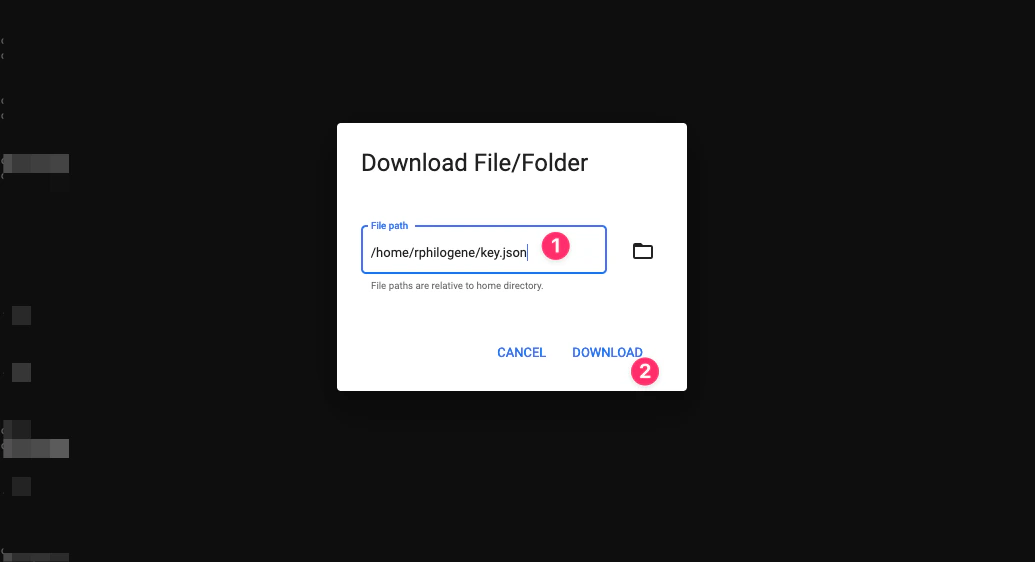
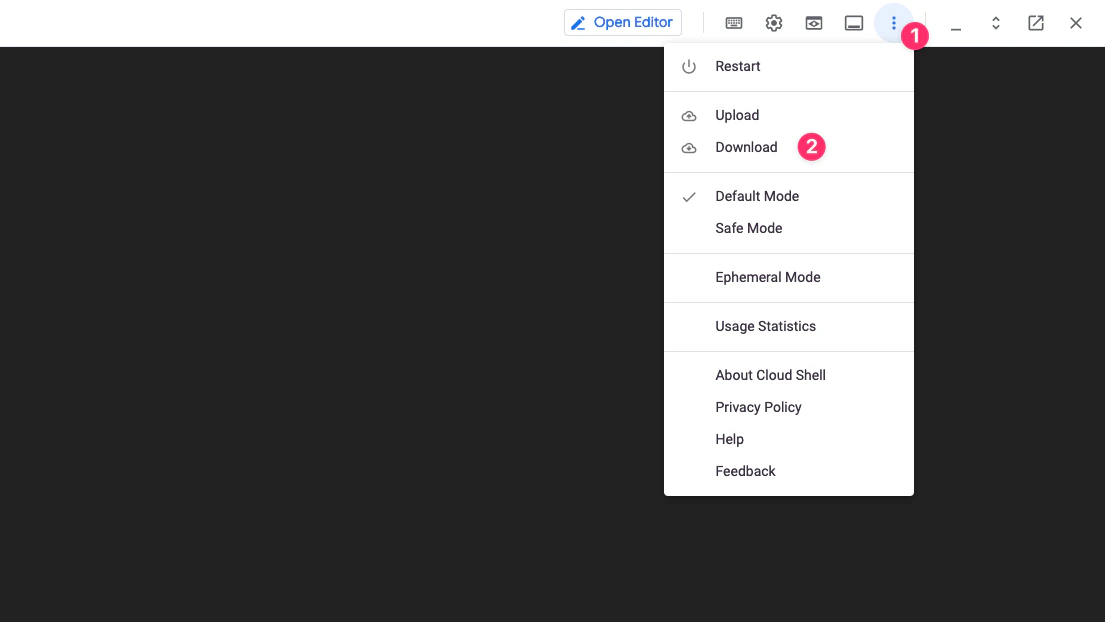
Download the Key File
- In Cloud Shell, click the More menu (three dots)
- Select Download
- Enter the file path:
key.json - Save the file securely
What permissions does Qovery need?
What permissions does Qovery need?
Qovery requires these GCP permissions to manage your infrastructure:
- Compute Engine: Create and manage VMs, networks, and load balancers
- Kubernetes Engine: Create and manage GKE clusters
- VPC Networking: Configure networks, subnets, and firewall rules
- Service Accounts: Manage service identities for workloads
- Cloud Storage: Store Terraform state and logs
- Artifact Registry: Store container images
- Cloud Run: Manage serverless deployments (optional)
compute.addresses.* permissions to reserve external IPs.The installation script automatically assigns the minimum required roles to the service account.Can I use a custom service account?
Can I use a custom service account?
Yes! You can create a service account manually with custom permissions.
However, ensure it has all the roles required for managing GKE, Compute
Engine, and networking resources. Contact support for the minimal permissions
list.
How do I rotate credentials?
How do I rotate credentials?
To rotate GCP credentials:
- In GCP Console, go to IAM & Admin → Service Accounts
- Find the
qovery-service-account - Click Keys → Add Key → Create new key
- Choose JSON format and download
- Update credentials in Qovery Console
- Wait 24 hours, then delete the old key in GCP
Create the Cluster
Select GCP as Hosting Mode
Click on
GCP as hosting mode and then Qovery Managed option.In the Create Cluster window enter:- Cluster name: enter the name of your choice for your cluster.
- Description: enter a description to identify better your cluster.
- Production cluster: select this option if your cluster will be used for production.
- Region: select the geographical area in which you want your cluster to be hosted.
- Credentials: select one of the existing cloud provider credentials or create new credentials.
Next.Configure Network
In the Use those two IPs as the source addresses to allowlist with your third-party providers.
Network step, select the network mode you want to enable on your cluster.If you want to manage the network layer of your cluster by yourself, you can switch VPC mode to Deploy on my existing VPC to use your own VPC instead of the one provided by Qovery.- VPC managed by Qovery
- Use your existing VPC
Static IP
The Static IP feature is currently only available to clusters deployed with a VPC managed by Qovery and can only be enabled at cluster creation.By default, when your cluster is created, its worker nodes are allocated public IP addresses, which are used for external communication. For improved security and control, the Static IP feature allows you to ensure that outbound traffic from your cluster uses specific IP addresses.Here is what will be deployed on your cluster:- Cloud Routers
- Cloud NAT gateways
- Auto-allocated Cloud NAT IPs (default) or two reserved external IPs per cluster (opt-in, see below)
Default behavior: auto-allocated Cloud NAT IPs
By default, the Cloud NAT gateways provisioned by Qovery use auto-allocated public IPs managed by GCP. These IPs can rotate over time (for example after maintenance, scaling events, or NAT reconfiguration) and are therefore not suitable for whitelisting with third-party services that require a fixed source IP.Opt-in: stable egress IPs via the NAT Gateway feature
To get stable egress IPs that you can safely allowlist with services like Stripe, payment gateways, or partner APIs, enable static Cloud NAT IPs on the cluster’s NAT Gateway feature. When configuring the NAT Gateway feature on your GKE cluster, set thestaticIpsEnabled option to true (default false). When enabled, the engine reserves two static external IPs (google_compute_address) per cluster and binds them to the Cloud NAT in MANUAL_ONLY mode. These IPs remain stable for the entire lifetime of the cluster.This option is configured alongside the other NAT Gateway parameters via the cluster’s NAT Gateway configuration in the Console, API, or Terraform provider. On the API and Terraform sides the field is named staticIpsEnabled on NatGatewayParameters (serialized as static_ips_enabled on the JSON wire format).Things to know before enabling:
- Cost: each reserved external IP is billed by GCP at about
$0.005/hour(~$3.65per IP per month), so two IPs add roughly$7.30/monthto your GCP bill per cluster. - GCP quota: GCP enforces a default quota of 8 reserved external IPs per region. Make sure your project quota can accommodate 2 IPs per GKE cluster region before enabling.
- Connection capacity: with
MANUAL_ONLY, GCP can no longer scale NAT IPs automatically. Simultaneous outbound connections are hard-capped at2 × 64512 / min_ports_per_vm. For most clusters this is well within the budget, but very high-traffic or multi-tenant clusters should validate.
Finding the reserved IPs once enabled
OncestaticIpsEnabled is on and the cluster has been applied, here is the procedure to find the IPs in the GCP console:- Select the project that hosts your Qovery cluster.
- Go to VPC network then External IP addresses.
- Filter by the region where your cluster is deployed.
- Look for the two reserved addresses named
${vpc_name}-nat-1and${vpc_name}-nat-2, with typeExternaland statusIn use byyour Cloud NAT gateway.
On AWS, NAT Gateways always require Elastic IPs (this is the only mode AWS supports), so Qovery-managed EKS clusters have stable egress IPs by default. You can find them in the AWS console under VPC then Elastic IP addresses. See Static IP on EKS for details.
Create and Install
In the
Ready to install your cluster window, check that the services needed to install your cluster are correct.You can now press the Create and Install button.Your cluster is now displayed in your organization settings, featuring the Installing... status (orange status). Once your cluster is properly installed, its status turns to green and you will be able to deploy your applications on it.You can follow the execution of the action via the cluster status and/or by accessing the Cluster LogsManaging your Cluster Settings
To manage the settings of an existing cluster:Open Qovery Console
Open your Qovery Console.
General
TheGeneral tab allows you to define high-level information on your cluster:
| Item | Description |
|---|---|
| Cluster Name | To edit the name of your cluster. |
| Description | To enter or edit the description of your cluster. |
| Production Cluster | To enter or edit the production flag of your cluster. |
Credentials
Here you can manage here the cloud provider credentials associated with your cluster. If you need to change the credentials:- generate a new set of credentials on your cloud provider (Procedure for GCP account)
- create the new credential on the Qovery by opening the drop-down and selecting “New Credentials”
Mirroring registry
In this tab, you will see that a container registry already exist (calledregistry-{$UIID}).
This is your cloud provider container registry used by Qovery to manage the deployment of your applications by mirroring the docker images.
The credentials configured on this registry are the one used to create the cluster. But you can still update them if you prefer to manage them separately (dedicated pair of creds just to access the registry).
Check this link for more information.
Network
TheNetwork tab in your cluster settings allows you to check if the Static IP, Deploy on existing VPC features are enabled on your cluster. The enabled features cannot be changed after the creation of the cluster.